A colleague of mine — a senior network engineer at a mid-sized fintech firm — told me something that stuck with me over coffee last month. He said, “We spent three years building the perfect perimeter firewall. Then one phishing email from a contractor completely bypassed it. Three years. Gone.” That single sentence captures exactly why Zero Trust isn’t just another buzzword being thrown around in vendor slide decks. It’s a fundamental rethinking of how we approach trust in modern infrastructure.
So let’s dig into what Zero Trust actually means in 2026, where the technology has evolved, and — most importantly — what it looks like when you’re actually trying to implement it in the real world (spoiler: it’s messier than the whitepapers suggest).
What Zero Trust Actually Means (Beyond the Marketing Fluff)
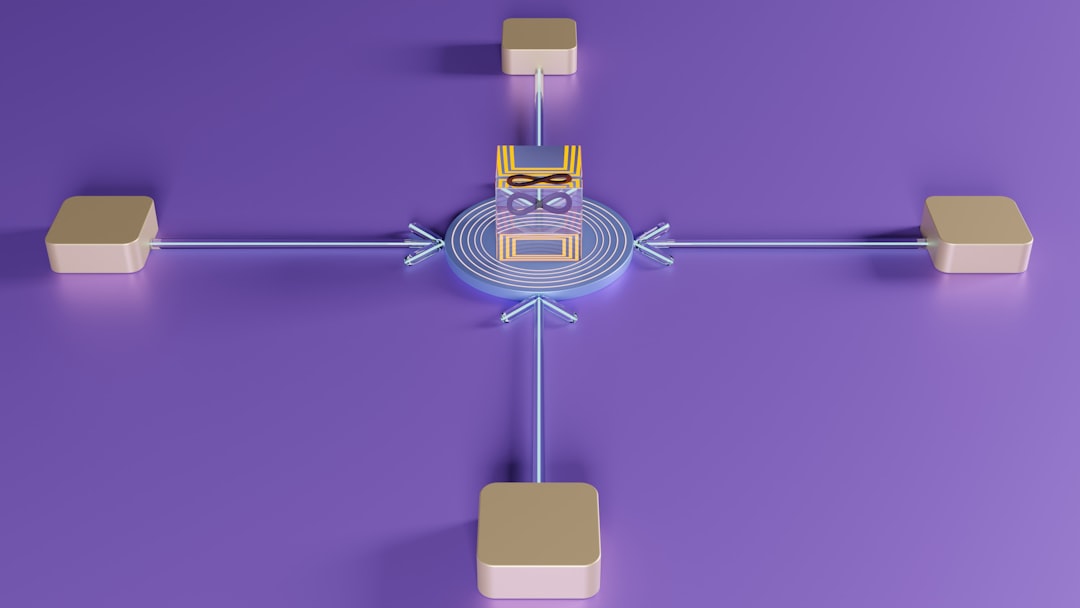
The core principle, first articulated by John Kindervag at Forrester back in 2010, is deceptively simple: “Never trust, always verify.” But in 2026, that principle has evolved into something far more nuanced and technically demanding. Zero Trust Architecture (ZTA) now encompasses a multi-layered framework that includes:
- Identity-centric access control: Every user, device, and workload must continuously prove its identity — not just at login, but throughout the entire session.
- Micro-segmentation: Network segments are broken down to the workload level, so lateral movement after a breach is severely restricted.
- Least-privilege access: Users and systems get only the minimum permissions necessary to do their job — and those permissions expire.
- Continuous behavioral analytics: AI-powered systems monitor for anomalous behavior in real time, not just at the point of authentication.
- Device posture assessment: A device’s security health (patch level, EDR status, encryption state) is evaluated before granting access.
- Encrypted communications everywhere: East-west traffic inside the network is encrypted, not just north-south traffic at the perimeter.
The 2026 Threat Landscape: Why Zero Trust Is Non-Negotiable Now
Let’s look at some cold, hard numbers that make the case. According to IBM’s Cost of a Data Breach Report 2026, the average cost of a data breach globally has climbed to $5.3 million USD — up 18% from three years ago. More alarming? The average dwell time (how long attackers linger undetected inside a network) has actually increased despite greater awareness, largely because threat actors are now using AI-generated credentials and deepfake-assisted social engineering that bypasses traditional multi-factor authentication.
The shift to hybrid work — which is now essentially permanent across most enterprise sectors — has fundamentally broken the concept of a trusted internal network. According to Gartner’s 2026 Security Forecast, 78% of enterprise workloads now run in multi-cloud or hybrid environments, meaning the traditional castle-and-moat model isn’t just ineffective — it’s architecturally obsolete.
Nation-state actors and ransomware groups have also become dramatically more sophisticated. The CVE exploitation-to-weaponization window has shrunk from an average of 15 days (in 2022) to under 72 hours in 2026, according to data from CISA’s quarterly threat reports. If your security model relies on patching before attackers exploit a vulnerability, you’re already behind.
Where Zero Trust Tech Has Actually Evolved in 2026
This is where things get genuinely exciting from an engineering standpoint. The Zero Trust space has matured significantly, and we’re seeing convergence around a few key technological pillars:
1. AI-Driven Continuous Authentication (AICA)
Traditional MFA is increasingly being supplemented — or in some cases replaced — by behavioral biometrics and AI-driven continuous authentication. Systems from vendors like Okta, CrowdStrike, and Microsoft Entra ID (formerly Azure AD) now analyze keystroke dynamics, mouse movement patterns, and application usage rhythms in real time. If the behavior drifts outside your established baseline, access is challenged or revoked — automatically, mid-session.
2. SASE (Secure Access Service Edge) Maturation
SASE — which fuses network security functions (SWG, CASB, ZTNA, FWaaS) into a cloud-delivered service — has become the dominant delivery model for Zero Trust at the network layer. Players like Zscaler, Palo Alto Networks Prisma, and Netskope have continued to dominate this space. What’s new in 2026 is the deep integration of LLM-based threat intelligence into SASE platforms, enabling context-aware policy decisions that adapt in near-real-time.
3. Quantum-Resistant Cryptography Integration
With NIST having finalized its post-quantum cryptography standards (CRYSTALS-Kyber, CRYSTALS-Dilithium) in 2024, Zero Trust implementations in 2026 are starting to incorporate quantum-resistant key exchange protocols. This is especially relevant for government and critical infrastructure sectors. If you’re not thinking about “harvest now, decrypt later” attacks in your threat model, you should be.
4. Identity Threat Detection and Response (ITDR)
This is one of the hottest emerging categories in 2026. ITDR platforms specifically focus on detecting attacks targeting identity infrastructure — Active Directory compromise, Kerberoasting, Golden Ticket attacks, etc. Vendors like Semperis and Quest Software have built dedicated ITDR platforms, while broader XDR vendors are rapidly integrating these capabilities.

Real-World Case Studies: Zero Trust in the Wild
Google BeyondCorp (The OG Case Study): Google’s internal implementation of Zero Trust — documented in their BeyondCorp research papers and now available as a commercial product (BeyondCorp Enterprise) — remains the gold standard reference architecture. By 2026, BeyondCorp Enterprise has been adopted by over 3,000 enterprise customers globally, and Google has published detailed migration playbooks at cloud.google.com/beyondcorp.
U.S. Federal Government Mandate: Following the Biden administration’s 2021 Executive Order on cybersecurity, U.S. federal agencies were required to adopt Zero Trust architectures by the end of FY2024. CISA published the Zero Trust Maturity Model 2.0 to guide this transition. As of early 2026, the DoD has completed Phase 2 of its Zero Trust implementation across most classified and unclassified networks — a massive, real-world proof point that ZTA can scale to extremely complex environments.
South Korean Financial Sector (K-Fintech ZTA Initiative): South Korea’s Financial Services Commission (FSC) mandated Zero Trust compliance for all Tier-1 financial institutions by Q4 2025. The rollout — involving institutions like Kakao Bank and KB Financial Group — required deep integration of ZTNA with existing legacy core banking systems. The lessons learned (particularly around micro-segmentation of COBOL-based mainframe environments) are being documented by KISA (Korea Internet & Security Agency) and will be published as public guidance documents in mid-2026.
The Hard Truth: Common Implementation Pitfalls
Look, I’m not going to pretend this is easy. From an engineer’s perspective, Zero Trust implementation is genuinely hard, and here’s where I see teams stumble most often:
- “Big Bang” deployment attempts: Trying to implement full ZTA overnight almost always fails. The successful implementations I’ve seen adopt a phased approach — start with identity, then devices, then network segmentation, then data classification.
- Neglecting legacy systems: Your Zero Trust policies are only as strong as your weakest asset. That Windows Server 2012 box running the legacy ERP system? It needs to be in scope, even if integration is painful.
- Poor user experience design: If Zero Trust makes people’s jobs significantly harder, they’ll find workarounds — and those workarounds create the vulnerabilities you’re trying to prevent. UX is a security concern.
- Incomplete asset inventory: You can’t protect what you don’t know exists. Shadow IT and unmanaged devices are the Achilles heel of most ZTA implementations.
- Treating it as a product, not a strategy: No single vendor gives you Zero Trust. It’s an architectural philosophy that requires coordinating policies across multiple tools and teams.
Realistic Roadmap for Teams Starting in 2026
If your organization is just beginning its Zero Trust journey, here’s a pragmatic starting framework rather than an overwhelming overhaul:
- Month 1-3: Complete asset and identity inventory. You cannot skip this. Use tools like Microsoft Defender for Endpoint or Axonius for asset discovery.
- Month 3-6: Implement phishing-resistant MFA (FIDO2/passkeys) across all privileged accounts and external-facing systems first.
- Month 6-12: Deploy ZTNA to replace legacy VPN for remote access. This is often the highest ROI early win.
- Year 2: Begin micro-segmentation initiatives, starting with crown jewel assets (financial systems, PII databases, IP repositories).
- Year 2-3: Integrate ITDR capabilities and begin behavioral analytics at the identity layer.
The NIST SP 800-207 framework (Zero Trust Architecture) remains the best publicly available reference document for planning purposes and can be downloaded free from csrc.nist.gov.
Editor’s Comment : Zero Trust isn’t a destination — it’s an ongoing operating model. The engineers and security teams thriving in 2026 aren’t the ones who’ve “implemented Zero Trust” and moved on. They’re the ones who’ve embedded the philosophy of continuous verification and least privilege into their organizational culture and daily engineering decisions. If you’re overwhelmed by the scope of it all, remember: start with identity, move methodically, and measure everything. The perimeter is dead — but the engineers who embrace that reality will be the ones building the secure infrastructure of the next decade.
📚 관련된 다른 글도 읽어 보세요
- 2026 AI 기술 트렌드 전망: 지금 알아야 할 5가지 핵심 변화
- 6G Technology in 2026: Where Are We Really, and When Will It Hit Your Pocket?
- Beyond the Smartphone: 7 Post-Smartphone Technologies Reshaping Daily Life in 2026
태그: Zero Trust Architecture, Cybersecurity Trends 2026, ZTNA Implementation, Identity Security, SASE Technology, AI Cybersecurity, Network Micro-segmentation
