Remember when 4G felt like magic? Suddenly streaming a full HD movie on a bus didn’t feel absurd anymore. Then 5G rolled in and promised us a hyper-connected world — and while it delivered in some areas, many of us are still waiting for that ‘revolutionary’ promise to fully land in our daily lives. Now, the conversation has already shifted to 6G, and honestly, the scale of what’s being discussed is something else entirely.
In early 2026, I attended a telecom futures panel where an engineer casually mentioned that 6G wouldn’t just be ‘faster 5G’ — it would fundamentally change the relationship between the physical and digital worlds. That stuck with me. So let’s dig into what’s actually happening in 6G development right now, look at real-world examples from around the globe, and think through what this means for everyday people — not just tech insiders.

📡 So What Exactly Is 6G — And Why Are We Talking About It Already?
6G refers to the sixth generation of mobile network technology, expected to reach commercial deployment somewhere between 2030 and 2035. But the groundwork — research, spectrum allocation, standardization — is being laid right now, in 2026. This is exactly the phase where 5G was being debated a decade ago, and decisions made today will shape the infrastructure of tomorrow.
Here’s what makes 6G fundamentally different from its predecessor:
- Speed: Theoretical peak speeds of 1 Tbps (terabit per second) — roughly 100x faster than 5G’s theoretical max of 20 Gbps.
- Latency: Sub-millisecond latency (targeting under 0.1ms), compared to 5G’s ~1ms. This matters enormously for real-time applications like remote surgery or autonomous vehicle coordination.
- Frequency Bands: 6G is expected to use terahertz (THz) spectrum (between 100 GHz and 10 THz), a range that’s currently largely unused but incredibly data-dense.
- AI Integration: Unlike previous generations, 6G is being designed from the ground up with native AI/ML capabilities embedded into the network architecture itself.
- Energy Efficiency: Targets a 100x improvement in energy efficiency per bit compared to 5G — a crucial consideration given global sustainability goals.
- Sensing + Communication Fusion: 6G networks won’t just transmit data — they’ll also act as environmental sensors, enabling real-time 3D mapping of physical spaces.
🌍 Who’s Leading the Race? Global 6G Development in 2026
The 6G development landscape in 2026 is intensely competitive, with governments treating it as a matter of national strategic interest — not just a telecom upgrade.
South Korea is arguably the most aggressive player right now. The Korean government launched its 6G R&D Promotion Strategy back in 2021 and has since funneled over $200 million USD into foundational research through agencies like ETRI (Electronics and Telecommunications Research Institute). By 2026, Korean researchers have successfully demonstrated THz-band data transmission over short distances with prototype hardware, and Samsung and LG Uplus are deeply embedded in international standardization bodies like ITU-R and 3GPP.
China launched its IMT-2030 (6G) Promotion Group in 2019 and has been publishing white papers at a staggering pace. Chinese companies — particularly Huawei, ZTE, and state-backed research institutes — have filed a significant portion of early 6G patents globally. As of early 2026, China holds an estimated 40%+ of early-stage 6G patent filings, though the quality and implementability of those patents vary widely.
The European Union has been channeling 6G efforts through the Hexa-X-II project (a successor to Hexa-X), a €250 million consortium involving Nokia, Ericsson, and dozens of universities. The EU’s approach emphasizes open, interoperable architectures and sustainability — essentially trying to make sure 6G doesn’t become another proprietary ecosystem battle.
The United States, through the FCC, NIST, and DARPA, has been funding 6G research with a strong focus on spectrum security and AI-native networking. The Next G Alliance (part of the Alliance for Telecommunications Industry Solutions) has been coordinating a North American roadmap, with companies like Qualcomm, Apple, and Google filing 6G-related patents at an accelerating clip.
Japan set an ambitious target to deploy 6G commercially by 2030, and NTT’s IOWN (Innovative Optical and Wireless Network) initiative is considered one of the most technically sophisticated national 6G frameworks, with particular emphasis on photonic networking and ultra-low power consumption.

🔬 The Technical Hurdles Nobody Talks About Enough
Here’s where I want to be honest with you, because a lot of 6G coverage tends to be either breathlessly optimistic or vague. The real challenges are significant:
- THz signal propagation: Terahertz waves are easily absorbed by moisture, walls, and even human bodies. Coverage range is extremely short — we’re talking meters, not kilometers in some bands. Solving this likely requires dense networks of intelligent reflective surfaces (called Reconfigurable Intelligent Surfaces or RIS).
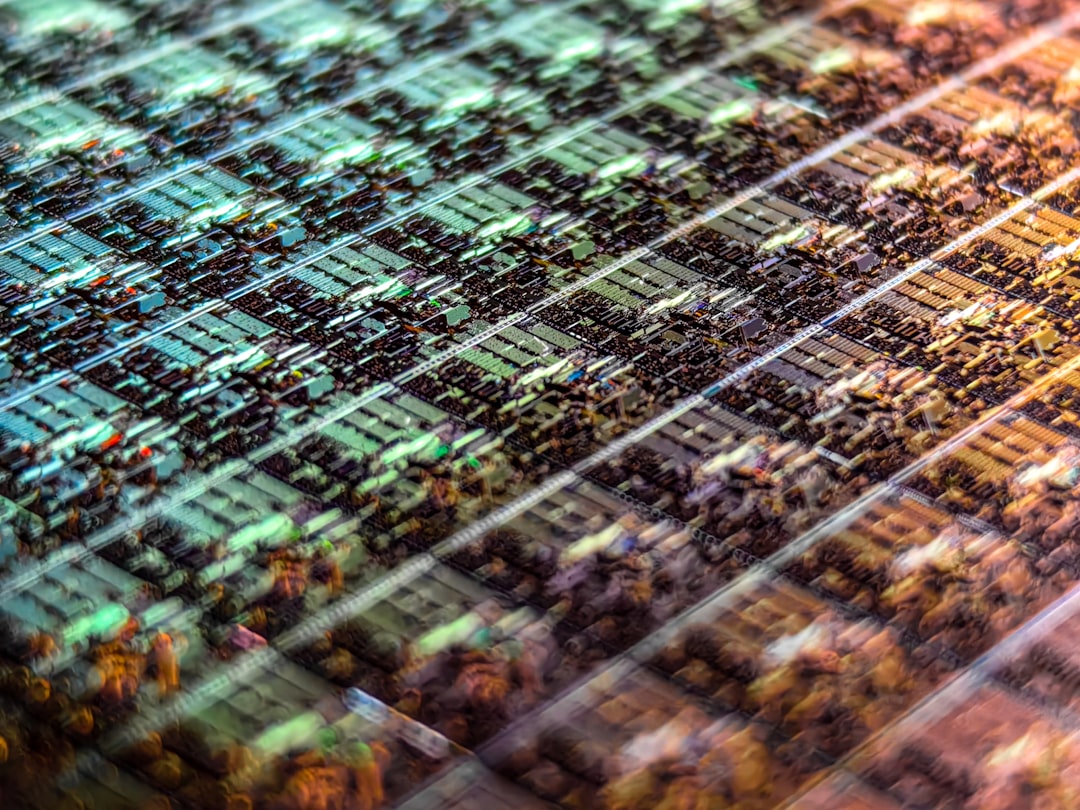
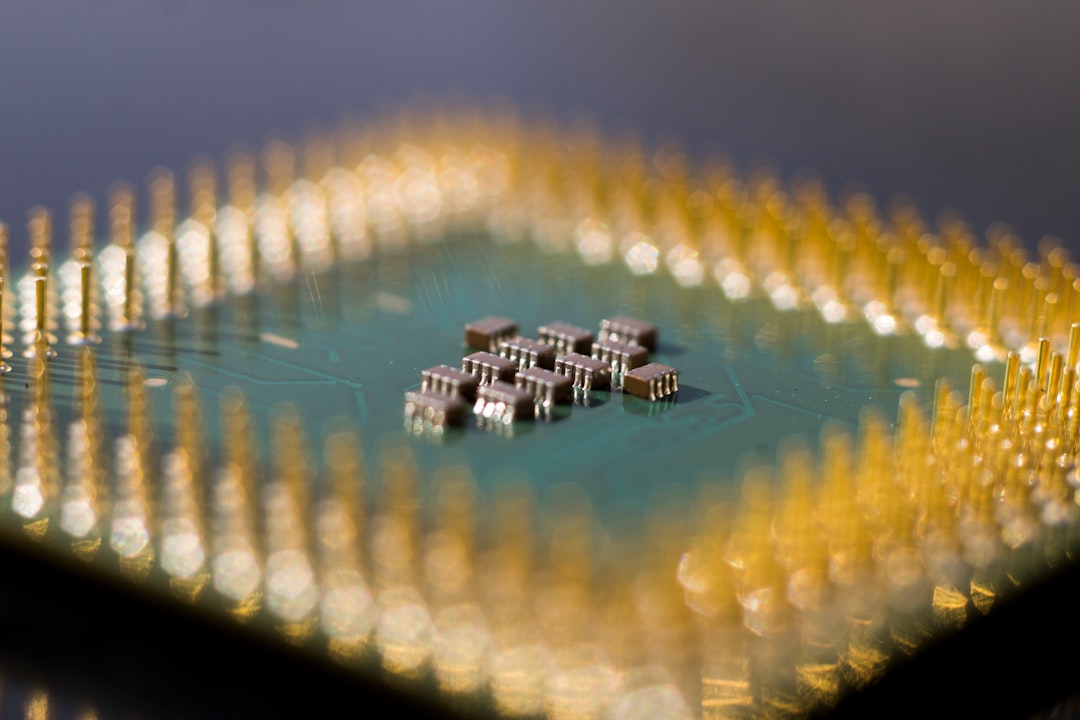
- Hardware immaturity: Devices capable of processing THz-band signals at consumer scale simply don’t exist yet at manufacturable costs. This is a 2028–2030 problem, but investment decisions are being made now.
- Spectrum allocation conflicts: The THz band overlaps with atmospheric sensing frequencies used by meteorologists and climate scientists. There are real, ongoing negotiations about who gets what.
- Standardization fragmentation: With the US, China, EU, and others each pushing their own technical frameworks, the risk of incompatible 6G ecosystems is non-trivial — which would be a massive problem for a globally connected world.
- Energy infrastructure: Even with efficiency improvements, the sheer density of 6G base stations needed could increase total network energy consumption significantly unless powered by renewables.
💡 What Does This Actually Mean for Regular People?
Let’s be realistic here. If you’re not a network engineer or a policy wonk, 6G might feel distant and abstract. And honestly? In 2026, it still is — for most consumers. But here’s why it matters to think about it now:
The applications being designed around 6G are already reshaping industries. Think about holographic communication (actual 3D holograms in meetings, not just VR headsets), fully autonomous transportation systems that require network reliability orders of magnitude beyond what 5G can provide, precision agriculture with real-time sensor networks across entire farms, and remote robotic surgery that becomes genuinely viable when latency is 0.1ms rather than 1ms.
For the average person, the most tangible near-term impact will likely come through trickle-down infrastructure improvements — better indoor coverage, more reliable IoT devices, and eventually, phones that don’t drop calls in an elevator. (A modest dream, but a valid one.)
🛤️ Realistic Alternatives: What If You Can’t Wait for 6G?
Here’s my practical take for businesses and individuals trying to make technology decisions today:
- For businesses: Don’t delay digital transformation waiting for 6G. Invest in robust 5G infrastructure now — the architectural lessons will translate. Look for 5G Advanced (sometimes called 5.5G) deployments, which are rolling out in 2026 and offer meaningful intermediate improvements.
- For developers and entrepreneurs: Build applications that leverage current 5G capabilities (edge computing, network slicing, URLLC for ultra-reliable low-latency communication) — these skills and concepts will be directly transferable to 6G environments.
- For individuals: Focus on what connectivity enables rather than the generation number. A well-optimized 5G network in your city will deliver better real-world performance than theoretical 6G specs on paper.
- For investors: The 6G supply chain — semiconductor companies, antenna technology firms, photonics specialists — is where early positioning makes sense, rather than trying to pick winner operators.
The 6G story in 2026 is fundamentally a story about preparation — nations, companies, and researchers laying foundations for a technology that will mature over the next decade. The decisions being made in labs and standards bodies right now will echo through the 2030s. And understanding the landscape today means you won’t be caught off guard when 6G stops being a buzzword and starts being your actual network signal.
Editor’s Comment : What excites me most about 6G isn’t the raw speed numbers — it’s the idea of a network that genuinely understands its environment and adapts intelligently. We’ve spent decades building communications infrastructure that moves data fast; 6G might be the first generation that actually thinks alongside us. That said, the gap between research promise and everyday reality is always wider than headlines suggest. Keep your expectations grounded, stay curious, and watch the standardization process — that’s where the real story unfolds.
태그: [‘6G technology 2026’, ‘6G development trends’, ‘next generation wireless network’, ‘6G vs 5G comparison’, ‘terahertz communication’, ‘6G global race’, ‘future connectivity technology’]